By popular request, here’s an explanation of the different encryption keys that are used on the Wii.
AES Keys: The Wii uses 128-bit (16-byte) symmetric AES (aka AES-128-CBC) for most encryption.

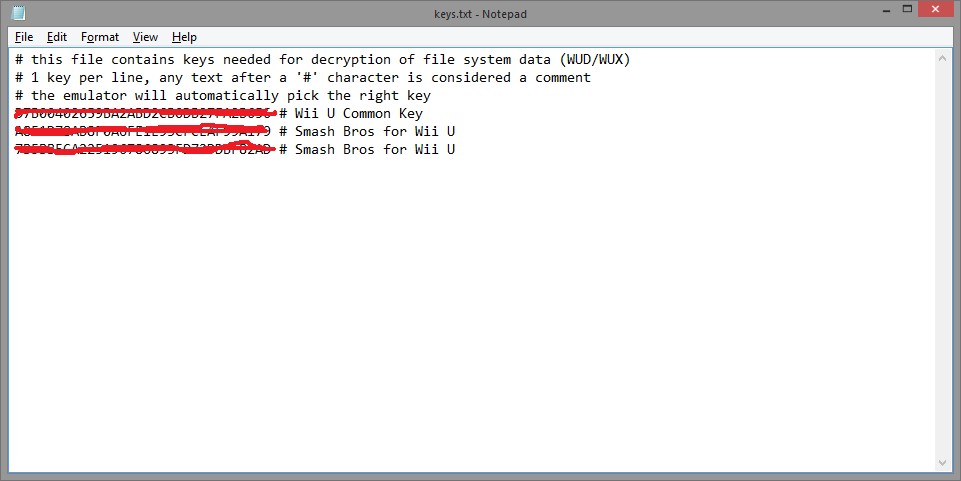
- Common key (ebe42a225e8593e448d9c5457381aaf7): This is the “shared secret” that we extracted with the Tweezer Hack. This key is known by all Wiis, but is never used, directly, to encrypt anything. Instead, all titles are encrypted with a random AES key; this key is then encrypted with the Common key and then stored inside a ticket. The ticket is then transmitted along with the content — on discs, it’s part of the “certificates” found before the encrypted data starts. Thus, knowing the common key allows you to decrypt most Wii content, as long as you have the right ticket. This key is stored in the OTP area inside the Starlet ARM core inside the Hollywood package.
- SD key (ab01b9d8e1622b08afbad84dbfc2a55d): This is another shared secret — also stored on the Hollywood, but also found plenty of other places, including inside the firmware images. This key is used by the System Menu (1-2) to encrypt anything before writing it out to the SD card, and it’s used by 1-2 to decrypt anything read from the SD card. This is done mainly for the purpose of obfuscation, to keep people from examining savegames. It’s worth noting that all Wii games save their data to the internal NAND — no game supports loading or saving data directly to SD. This frees game writers from the requirement of handling this step themselves; they just write the savegame data, unencrypted and unsigned, to their title-data directory inside the NAND filesystem; the system menu then handles everything else. (The real reason for this is probably that it allowed Nintendo to make a system where they didn’t have to expose the details of this encryption — or any encryption — to their licensed game developers.) This key is also stored in OTP, and in several places in IOS (for no apparent reason). If you’re using Segher’s tools, you may also be interested in the SD IV (216712e6aa1f689f95c5a22324dc6a98) and the MD5 blanker (0e65378199be4517ab06ec22451a5793), both of which are stored inside the 1-2 binary.
- NAND key (varies): This AES key is used to encrypt the filesystem data on the actual NAND chip itself; it is probably randomly generated during manufacturing and is also stored in the OTP area of the Starlet. This key is used to prevent the contents of the NAND filesystem from being read using a flash chip reader. Nintendo may or may not actually record this key anywhere, since they (theoretically) don’t need to ever use it. In fact, in some similar systems, keys like this are generated automatically by the device itself and (theoretically) never leave it — the Wii shares some design prinicples with HSMs, but it certainly doesn’t manage to be one. This is another OTP key.
RSA keys: The Wii uses RSA-based authentication in several different places. This is fundamentally different than the AES encryption used for data-hiding, because RSA is an asymmetric cipher, meaning there are no shared secrets — nothing to be extracted from the Wii. The only RSA keys stored on the Wii are public keys, used to verify authenticity of content.

- CP: Content Protection? This key is used to sign the TMD associated with every title. The TMD contains a SHA1 hash of the contents of that title, proving that it had not been modified. My 24c3 presentation was done by injecting a new .DOL into a Lego Star Wars disc and then forging the signature on its TMD, using a flaw originally discovered by Segher. After that presentation, people eventually discovered the common key needed to decrypt update partitions, allowing others to analyze / disassemble IOS. xt5 (who I had the pleasure of meeting at 24c3) was then able to find the same flaw and implemented it in his Trucha Signer. In fact, from disassembling his code, the core part of it was almost identical to our never-released code — great minds think alike, eh?
- XS: “Access”? This is the key that signs tickets, which contain the title keys for individual titles.
- CA: Certification Authority: This key signs both the XS and CP keys.
- MS: “Master?” This key is used to sign the certificate that contains a copy of your Wii’s public ECC key. This certificate is then appended to savegames on SD cards, so that any other Wii can verify that the key was issued by Nintendo.
- Root: This is the “grand master key”, which signs the CA key. The public half of this can be found here.
ECC keys: The Wii uses Elliptic Curve Cryptography in a few select places — primarily, it uses this when it signs savegames before writing them to SD card. ECC is used in ways similar to RSA, but it’s somewhat newer and much faster to run on an embedded system.
Alternatively enter Wii common key (32 characters) here: Common Key: Optional: Adjust Wii channel data here: Channel ID: Channel Title: Note: If you have multiple OoTR WAD files with different Channel IDs installed, the game can crash on a soft reset. Use a Title Deleter to remove old WADs.

- You can brick your Wii without it! 1) 'common-key.bin' in Loadstructor's folder. 2) USB mass storage device with WBFS partition. Recommented to use.
- The first thing we need to do is to generate a common-key.bin. To do this, go to Tools Create Common key. Type the text it asks you to type and press OK. Now go to Edit Preview. A new Window will pop-up with one image of the banner of the Wad.
Other: For lack of a better place to put it, there is also an HMAC key — a 20-byte value that is used in a SHA1-based HMAC of the NAND flash contents to prevent them from being tampered with. This is a commonly used scheme in embedded systems, where a device wants to “sign” something itself, for itself. There are no public vs private keys here — you need to know this value in order to verify the hash, and you need the same value to generate the hash. This isn’t appropriate for communications between two people, but is perfectly fine for letting the Wii test to see if the chip was pulled, rewritten, and resoldered.
Key storage: The public keys are stored in various places — these aren’t sensitive, so they don’t really need to be concealed (although at least one of them needs to be protected from modification, and it can then sign the others). The rest are stored in two places:
- Hollywood SEEPROM: After meeting him at 24c3, bunnie was kind enough to decap some chips for me, including a Hollywood. One of those chips is 2kbit serial EEPROM, which stores the MS signature on the the ECC key.
- One-Time Programmable Area: Inside the Starlet ARM core, there are a bunch of things:
- SHA1 hash of boot1
- Common key
- ECC private key
- NAND HMAC
- NAND AES key
- RNG seed
- other stuff we can’t yet decipher
Wii Common Key Download

Wii Common Key Bin Download